Microsoft Local Administrator Password Solution (LAPS) is a password manager solution that allows you to manage local administrator account passwords for Windows domain-joined devices. Passwords are generated dynamically and also constantly updated basis on the policies adopted; also passwords are saved within your Active Directory infrastructure and protected by ACLs, so that only authorized users can read or request a reset.
Microsoft LAPS also allows to improve the company’s security posture by reducing the surface from cyberattacks; in particular, the solution mitigates the risk of lateral escalation when all systems use the same password for the local administrator account.
Another plus of this solution is the full integration with your own AD infrastructure without the need for additional systems, interfaces, etc..
In this article, I will provide the information you need to implement the solution.
Active Directory Schema extension
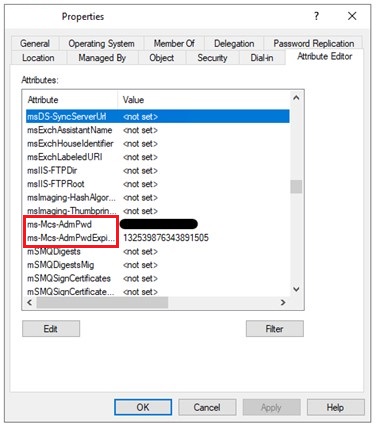
The first step in activating the solution is the AD Schema extension which allows you to add 2 new attributes:
- ms-Mcs-AdmPwd: attribute where the password is stored in clear text;
- ms-Mcs-AdmPwdExpirationTime: attribute where the password expiration timestamp is stored
To do this you need to follow these steps:
- From a management system, download the appropriate MSI installer based on your platform (LAPS.<platform>.msi).
- Run the MSI with administrative privileges.
- Accept terms and conditions.
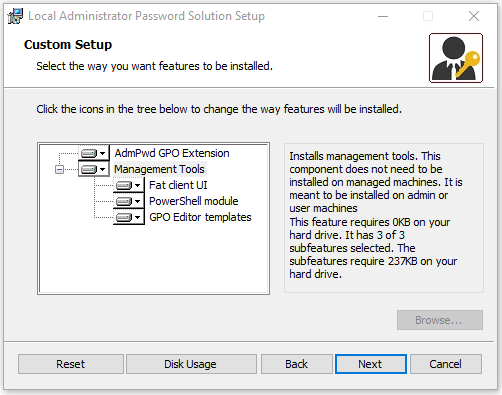
- Select all the features as screeshot below.
- Press Next button and complete the installation.
- After setup has completed successfully, open a Powershell window with administrative privileges.
- Execute the following command to import LAPS module (no output will be shown):
Import-module AdmPwd.PS
- To update AD Schema execute the following command:
Update-AdmPwdADSchema
- The operation will be completed correctly when each step will report the Success status.

Permission
To allow the various computer accounts to save/update the password and the expiration timestamp present on the AD, it is necessary to assign write permission on these attributes to the SELF account. This operation can be done using the Powershell module imported previously and executing the following command:
Set-AdmPwdComputerSelfPermission -OrgUnit <OU name to delegate permissions>
You must repeat this procedure for all OUs that contain computer accounts that are in scope of the solution and are not subcontainers of already processed containers.
As mentioned above, you can set ACLs on these attributes to allow only specific users to be able to read or request a password reset. The possibility of giving granular permissions allows you to differentiate the various environments (eg: client and server) and allow IT admins to provide the appropriate permissions to the various IT employees based on their scope; for example I can specify an AD group for client password management and one for server password management.
To assign the rights to read stored passwords, you need to execute the following command in a Powershell window with administrative privileges:
Set-AdmPwdReadPasswordPermission -OrgUnit <OU name to delegate permissions> -AllowedPrincipals <AD users or AD groups>
To assign the rights to force password resets, you need to execute the following command in a Powershell window with administrative privileges:
Set-AdmPwdResetPasswordPermission -OrgUnit <OU name to delegate permissions> -AllowedPrincipals <AD users or AD groups>
Group Policy
LAPS solution installs GPO templates that implement UI for setting configuration options; ADMX templates are installed into %SystemRoot%\PolicyDefinitions folder.
In case your organization uses centralized policy store (ADMX templates stored in SYSVOL), you must copy the ADMX templates into central policy store in SYSVOL.
Once the .admx files have been copied, it is necessary to proceed with the creation of a new GPO that will allow the LAPS client to set the local administrator password according to the specifications indicated; to do this you need to follow these steps:
- From your domain controller or from a management system, open Group Policy Management snap-in;
- Create a new Group Policy Object;
- Assign a name based on you naming convention;
- Edit the new created GPO;
- Access the section Computer Configuration\Administrative Templates\LAPS and set the following settings:
- Enable local admin password management: Enabled
This setting allows the LAPS client to manage the local admin password. - Do not allow password expiration time longer than required by policy: Enabled
This setting not allows to set planned password expiration longer than password age provided by Password Settings policy. - Password Settings:
- Password Complexity: Large letters + small letters + number + special
- Password Length: 14
- Password Age (Days): 30
This setting allow the LAPS client to configure password parameters.
- Enable local admin password management: Enabled
- Close the GPO window and link it to the interested Organizational Unit;
After carrying out these activities, it is necessary to proceed with the distribution of the LAPS client on the affected systems; this activity can be carried out through your management tool (ex: Configuration Manager) or through a specific GPO. The command line to use to install the LAPS client in silent mode is the following:
msiexec /i “LAPS.<platform>.msi” /q
Password Recovery
After the GPO is successfully applied on systems, there are a few ways to get the current local Administrator password:
- Using LAPS Fat client UI;
- LAPS Powershell Module;
- Active Directory User and Computers snap-in;
Through the installation of the Fat Client UI, it will be possible to retrieve the password of the local administrator from a specific graphic interface; to do this you need to follow these steps (if the LAPS client with all the features has already been installed on a management machine, these steps are not necessary):
- From a management system, run the LAPS Client MSI (LAPS.<platform>.msi) with administrative privileges.
- Accept terms and conditions.
- Select all the features as screeshot below.

- Finish the installation process by clicking on the Next button.
At the end of the installation process, a new software called LAPS UI will be available within Programs section; after starting the application, entering a computer name that you want to query the local Administrator password, the password in clear text and the expiration date is returned.
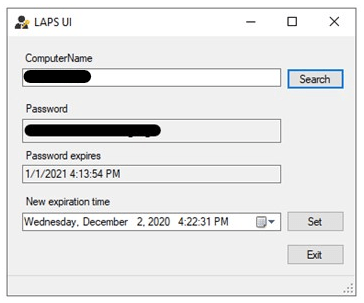
Using the Set button, you also have the capability to update the expiration date in this client.
You can also query this information using LAPS PowerShell module by executing the following command in a Powershell window with administrative privileges:
Get-AdmPwdPassword <Computer Name> | Out-Gridview
The last option to be able to recover the local administrator password is through the Attributes tab present in the Active Directory Users and Computers snap-in; to view this tab, you need to activate the Advanced View option of the snap-in (present in the View menu).
References
Here are some useful references to the official Microsoft documentation:
Conclusions
By using Microsoft LAPS, organizations will be able to simplify Local Administrator password management in order to implement additional defenses against cyber attacks.