In March and April, a considerable number of news regarding Microsoft Intune were announced by Microsoft. This blog, through these articles, wants to provide an overall overview of the main news, in order to stay up to date on these topics and have the necessary references to carry out more in-depth information.
Among the main innovations introduced in the latest versions, it is important to report the introduction of modern authentication in Apple Setup Assistant.
This feature was announced during the latest edition of Microsoft Ignite and consists of the ability to securely authenticate through Multi-Factor Authentication during the Setup Assistant screens.

For more information on how to use this type of authentication on Apple devices, refer to the following link.
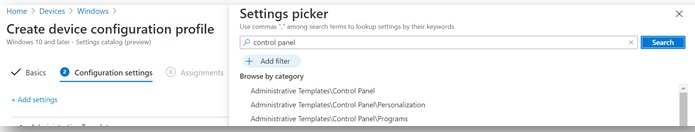
With a view to an increasingly stronger integration between the cloud world and the on-premise world, in recent months, the Intune Product Team has introduced a significant number of settings in the Settings Catalog section that were previously not available (currently in preview).
This operation made it possible to largely reduce the gap that appeared to be present between the MDM configurations and those through GPO; it also allowed companies to start taking a modern approach to managing their devices, thus also eliminating the need for connectivity with the on-premise environment).
In the next paragraphs, I will summarize the other important innovations introduced in recent months.
App management
Win32 App supersedence
It is now possible to define supersedence rules between Win32 apps to allow the updating or replace an application with a new version of the same app or with another application.
This mode was already present from various releases on Configuration Manager and is now available (in public preview) on Intune through the Microsoft Endpoint Manager admin center portal.
Still with regard to Win32 apps, in release 2104, a new field has been made available that allows you to view the version of the distributed application.
Maximum OS version condition within the Conditional Launch rules
Within the Conditional Launch rules available on the App Protection Policy, it is now possible to define the maximum operating system version through which users can connect to corporate resources; this configuration is useful for limiting access from pre-release or beta builds of the operating system. This condition is applicable on both Android and iOS devices.
Universal app of Microsoft 365 Apps and Intune Management agent
When the Microsoft 365 Apps or Intune Management agent is deployed through the Microsoft Endpoint Manager admin center portal, on Apple Silicon devices, the Universal app that works natively on this type of device will be distributed.
The same distribution will allow you to install the 64-bit version of the app on Mac systems based on Intel chips; Rosetta 2 appears to be a prerequisite for running the x64 (Intel) version of the apps on Apple Silicon devices.
Setup Microsoft Launcher app on Android Enterprise Fully Managed
With the use of an App Configuration Policy, it is now possible to set folder configurations in Microsoft Launcher on Android Enterprise devices registered in Fully Managed mode; it is therefore possible to configure the shape of the folder, the full screen opening and the scrolling direction.
New protected apps
The following protected apps appear to have been added on Microsoft Intune:
- FleetSafer (Cogosense Technology Inc.)
- Senses (Mazrica Inc.)
- Fuze Mobile for Intune (Fuze, Inc.)
- MultiLine for Intune (Movius Interactive Corporation)
- Omnipresence Go (Omnipresence Technologies, Inc.)
- Comfy (Building Robotics, Inc.)
- M-Files for Intune (M-Files Corporation)
Device Configuration
Improvement in Microsoft Edge management and configuration
Using the Settings Catalog, you can configure Microsoft Edge on a macOS device (Devices> Configuration profiles> Create profile> macOS for platform> Settings Catalog). As for Windows 10 devices configured in kiosk mode, it is now possible to allow only the Microsoft Edge application version 87 or later to run.
New version of PFX Certificate Connector
A new version (6.2101.16.0) of the PFX Certificate Connector has been released which fixes some bugs introduced in previous releases and prevents the creation of duplicate files related to certificate requests. For more details, you can refer to the following link.
Using Cisco AnyConnect as a VPN Profile
Within the VPN profiles that can be created through Intune on Windows 10 devices, it is now possible to select the Cisco AnyConnect solution. The deployment of this profile will install the Cisco AnyConnect app available on the Microsoft Store (desktop application is not used).
Disable NFC on iOS and iPadOS devices in supervised mode
On iOS and iPadOS devices registered in Supervised mode, it is possible to disable NFC through the adoption of a Device Restriction Policy (Devices> Configuration profiles> Create profile> iOS / iPadOS for platform> Device restrictions for profile> Connected devices> Disable near field communication ( NFC)).
Device enrollment
Sync status of registration tokens dedicated to the Automated device enrollment process
The synchronization status of the tokens dedicated to Automated Device Enrollment (ADE) mode have been removed from the Enrollment program tokens interface; ADE mode allows automatic registration of Apple devices using the Apple Business Manager or Apple School Manager services.
Within the admin center console (Devices> iOS / iPadOS> iOS / iPadOS enrollment> Enrollment program tokens – Devices> macOS> macOS enrollment> Enrollment program tokens), the ability to view the list of your tokens is still maintained.
Device management
Diagnostic log remote collection
Another very interesting news released in the 2102 version is the introduction of a new remote action called Collect diagnostics; through this action it is possible to remotely collect all the diagnostic logs useful for troubleshooting without interfering with the end user’s operation.
Below is a list of the logs/diagnostic information collected:
- MDM
- Autopilot
- Event Viewer
- Registry key
- Configuration Manager client
- Network configurations
- Certificates
- Windows Update
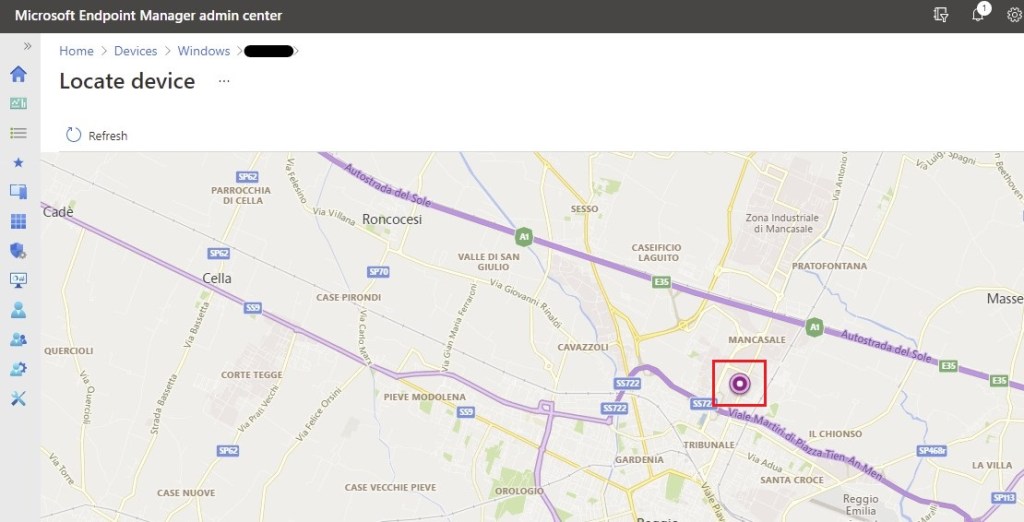
Locate device remote action for Windows 10 devices
Within the 2104 release, a new remote action called Locate device has been included which allows you to geolocate Windows 10 systems (like iOS devices registered in Supervised mode). A prerequisite for using this feature is the activation of the location service natively present on the operating system.
Once the remote action has been performed, the user will be notified, through a special toast notification, that the company has requested the location of their device. The systems that support this functionality are:
- Windows 10 version 20H2
- Windows 10 version 2004
- Windows 10 version 1909
- Windows 10 version 1809
Device Security
Use UserPrincipalName attribute when requesting certificates
On Android devices, it is now possible to use the CN = {{UserPrincipalName}} attribute as a parameter to be set in the subject field (or Subject Alternative Name field) when requesting a new certificate via PKCS or SCEP.
The requirement in order to use this attribute is that the device is registered in a way that contemplates user-affinity (eg: Fully Managed or personally-owned with work profile).
Use of Microsoft Defender for Endpoint within the App Protection Policy
It is now possible to use Microsoft Defender for Endpoint on Android and iOS devices within the App Protection Policy; by inserting the condition Max allowed threat level signals, it will therefore be possible to block access to corporate resources in the event that the device exceeds the set threat level.
If this condition is set, users will be prompted to install and configure the Microsoft Defender for Endpoint app. As a prerequisite in adopting this feature, you need to configure Microsoft Defender for Endpoint connector and activate the toggle to send risk data to the Protection Policy App.
Improvements in the detection rules present within the Attack Surface Reduction rule
It is now possible to use the rule called Block persistence through WMI event subscription within the Attack Surface Reduction rule; this rule prevents malware from abusing WMI to attain persistence on a device. Fileless threats employ various tactics to stay hidden, to avoid being seen in the file system, and to gain periodic execution control.
This rule can be configured in the following ways:
- Not configured (default) – The setting returns to the Windows default, which is off and persistence is not blocked.
- Block – Persistence through WMI is blocked.
- Audit – Evaluate how this rule affects your organization if its enabled (set to Block).
- Disable – Turn this rule off. Persistence is not blocked.
Prevent or authorize merge between Antivirus Policy
During the configuration of an Antivirus policy, it is now possible to define the behavior that must be applied if there are local exclusions on the device; it is possible to allow the merge or prevent this behavior by applying only the exclusions defined via policy.
Health status details for Microsoft Tunnel Gateway servers
Within the Tenant administration> Microsoft Tunnel Gateway> Health status section, you can view details on the health status of the Microsoft Tunnel Gateway such as:
- Last check-in – When the server last checked-in with Intune.
- Number of current connections – The number of active connections at last check-in
- Throughput – The megabits per second that traverse the serves NIC at last check-in.
- CPU usage – The average CPU use.
- Memory usage – The average memory use.
- Latency – The average time for IP packets to traverse the NIC.
- TLS certificate expiration status and days before expiration – How long the TLS certificate that secures client to server communication for the tunnel remains valid.
Tunnel client functionality in Microsoft Defender for Endpoint (Public Preview)
As announced in the latest edition of Microsoft Ignite, Microsoft Tunnel client functionality has been migrated/integrated into Microsoft Defender for Endpoint; with preview version of the application, you can use Microsoft Defender for Endpoint as a tunnel app on devices that support this feature (Android Enterprise Fully managed, Android Enterprise Corporate-owned work profile, Android Enterprise Personally-owned work profile).
Configurations for updating the Tunnel Gateway
In the latest release, some improvements have been introduced for the management of the Tunnel Gateway update; the options now available are:
- Maintenance Windows: allows you to define a maintenance window within the server can proceed with the update;
- Server upgrade type: it is possible to define the update type by selecting the following methods:
- Automatic – the server(s) will upgrade as soon as possible after a new server version becomes available.
- Manual – the server(s) will proceed with the update only after authorization from an IT Admin;
Monitor and troubleshooting
New experience in Endpoint Analytics
Starting from these latest releases, review and update activities have been carried out on Endpoint Analytics:
- Within Microsoft Productivity score, there is a new page linked to Endpoint Analytics that allows you to share the results at the organization level with other results not strictly related to Microsoft Endpoint Manager.
- A new report called Application Reliability has been introduced which provides information on potential problems related to desktop applications; this report also allows you to view metrics on the use of the individual application and also any errors generated.
- The Restart Frequency report is now available in Generally Available; through this report it is possible to view the frequency whereby the devices are restarted and thus identify problematic systems where continuous restarts occur due to blue screen.
